You may remember in early May 2021, headlines breaking across the world stating that the Colonial oil pipeline (the largest fuel pipeline in the U.S) had been taken offline during a hack. The real-world consequences of this attack led to fuel shortages across the East Coast of North America, as the company was unable to transport the usual daily amount of 100 million gallons of fuel across the area spanning Texas to New York.
Since then, the number of big ransomware attacks have also included meat processing giant JBS, Ireland’s health service, and Japanese multinational conglomerate Fujifilm. So how can these huge companies be forced to shut down by ransomware? Discover more below.
What is Ransomware?
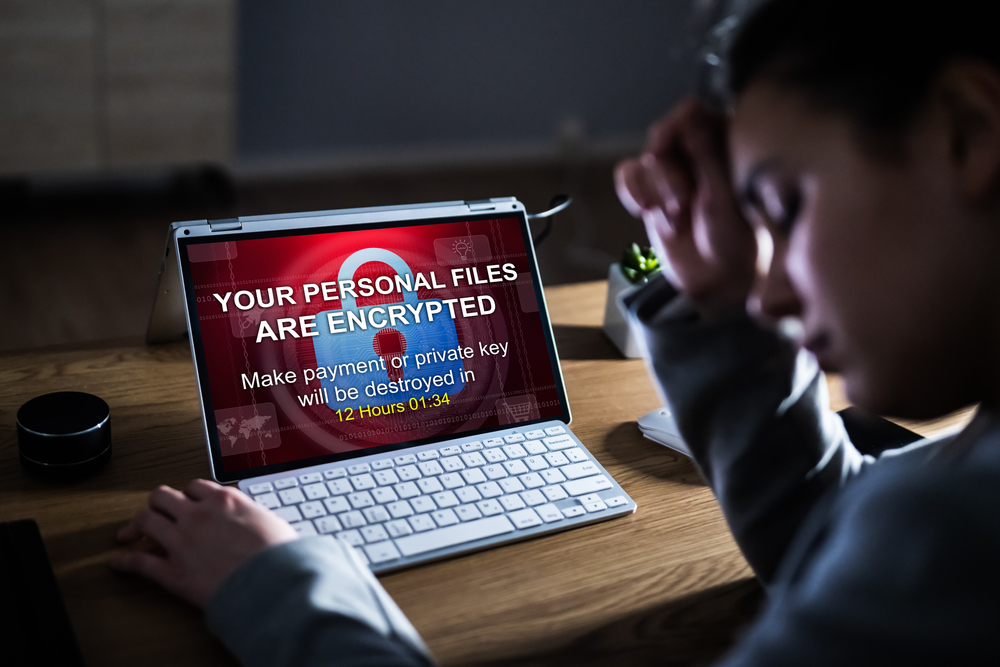
Ransomware is a form of malware that encrypts a victim’s files – making them completely unreadable to anyone but the hacker. Once the attack has been successfully carried out, the attacker then demands a ransom from the victim in order to restore access to the data upon payment.
To decrypt the files, users are shown instructions for how to pay the fee the attacker wants. The costs can range from a few hundred dollars to thousands, payable to cybercriminals in Bitcoin. In the case of the Colonial pipe hack, for example, attackers requested $4.4m (£3.1m) to be paid in Bitcoin.
How do attackers gain access to cybernetworks?
While the movies have made it seem like hackers need extensive knowledge of computer systems in order to guess passwords and break down cybersecurity walls, in reality it is actually much more simple to get hold of these passwords than you might think.
One of the most common ways the malware can be installed on a company system is through a phishing scam. In this case, workers at a company receive an email containing attachments, masquerading as a file they should trust. If the individual downloads and opens the files, the malware gets installed on the computer and from then an attack can remotely take over the whole network.
Sometimes, these emails also contain social engineering tactics. These encourage employees to type in their login credentials to access the file but it is the attacker who actually gains the username and password – giving them backend access to the entire security network.
Disgruntled employees have also been known to sell their login credentials to hackers on the dark web, or they can also be put on the dark web after an old cyberattack on the system. While it has not been confirmed this is what happened during the Colonial pipeline hack, Charles Carmakal, senior vice president at cybersecurity firm Mandiant, has said that the account credentials used in the attack were no longer in use at the time of the attack but could still be used to access Colonial’s network.
Who are the targets of ransomware?
Every organisation is a target for malware due to the fact most companies want to keep the details of an attack quiet – should they fall victim to one. Unlike when personal data is leaked from a company, enterprises are not required to notify customers about these sort of attacks and so in general pay the ransom to get immediate access back to their files before the press becomes aware.
Given this, it is important every organisation has a strategy in place determining how they will deal with a ransomware attack and what preventative measures they will take to avoid them. Some organisations and governments recommend not paying a ransom if the company falls victim to an attack, in case they invite further hacks in the future. Evidently though, this is a risky strategy if a company’s reputation is on the line and they need to get their systems up and running smoothly as quickly as possible to limit monetary damage.
On the other hand, there is no guarantee the organisation will get the decryption code even if they pay — or that it’ll work properly.
How to prevent ransomware
Preventing ransomware revolves around the implementation of two crucial steps:
- Educating employees on ransomware and teaching them the techniques attackers take to access computer networks.
- Keeping cybersecurity systems up-to-date.
The latter includes installing anti-virus software, using multi-factor authentication to confirm an employee logging into the network is really who they are claiming to be (especially when working from home) and installing regular updates when available to the network’s operating system.
Finally, data should be regularly backed up with versioning software. Versioning ensures that each backup of a computer is treated as a separate version, so if you happen to back up an infected file, you can “roll back” to an older version that’s not yet been infected.
What would you do if you fell victim to ransomware? Let us know in the comments section, and, if you have any questions or other technology queries, tweet us at @techtroublesho1.
2 thoughts